




























Stealthwatch Cloud is best known for network behavioral anomaly detection and entity modeling, but the level network visibility value it provides far exceeds these two capabilities. The underlying traffic dataset provides an incredibly accurate recording for every network conversation that has transpired throughout your global network. This includes traffic at remote locations and deep into the access layer that is far more pervasive than sensor-based solutions could provide visibility into.
Stealthwatch Cloud can perform policy and segmentation auditing in an automated set-it and forget-it fashion. This allows security staff to detect policy violations across firewalls, hardened segments and applications forbidden on user endpoints. I like to call this setting virtual "tripwires" all over your network, unbeknownst to users, by leveraging your entire network infrastructure as a giant security sensor grid. You cannot hide from the network...therefore you cannot hide from Stealthwatch Cloud.
Here is how we set this framework up and put it into action!




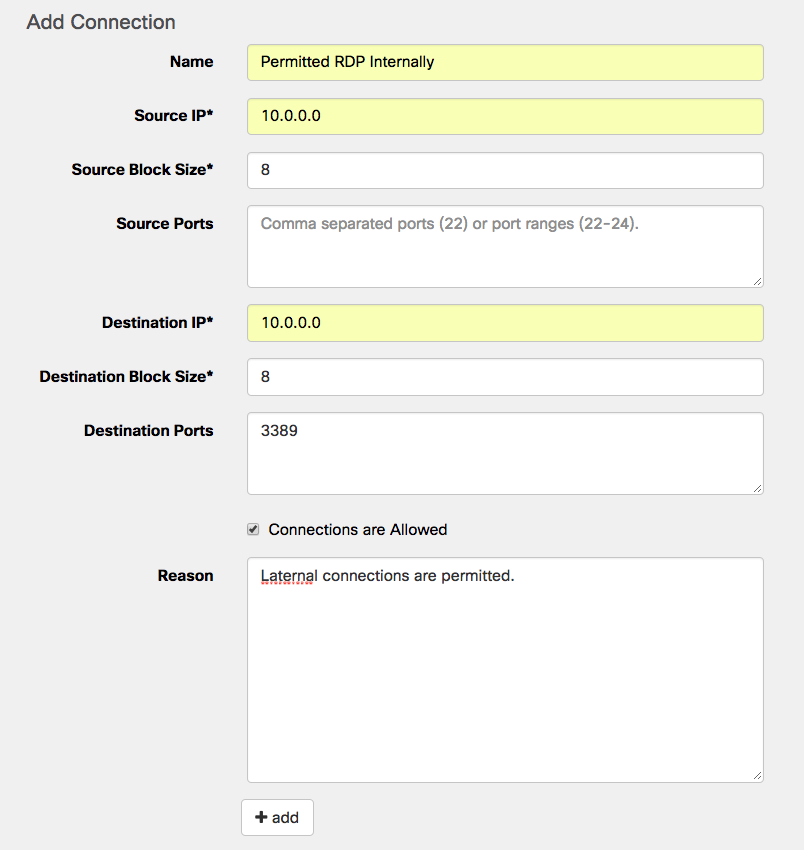
Destination IP: Target IP Address or CIDR range
Destination Block Size: CIDR notation block size, for example (0, 8, 16, 24, etc.)
Destination Ports: The target port traffic you wish to allow or disallow, for example (21, 3389, etc)
Connections are Allowed checkbox: Check this if this is the traffic you're going to permit. This is used in conjunction with a second rule to specify all other traffic that's not allowed.
Reason: Enter a user friendly description of the intent for this rule.



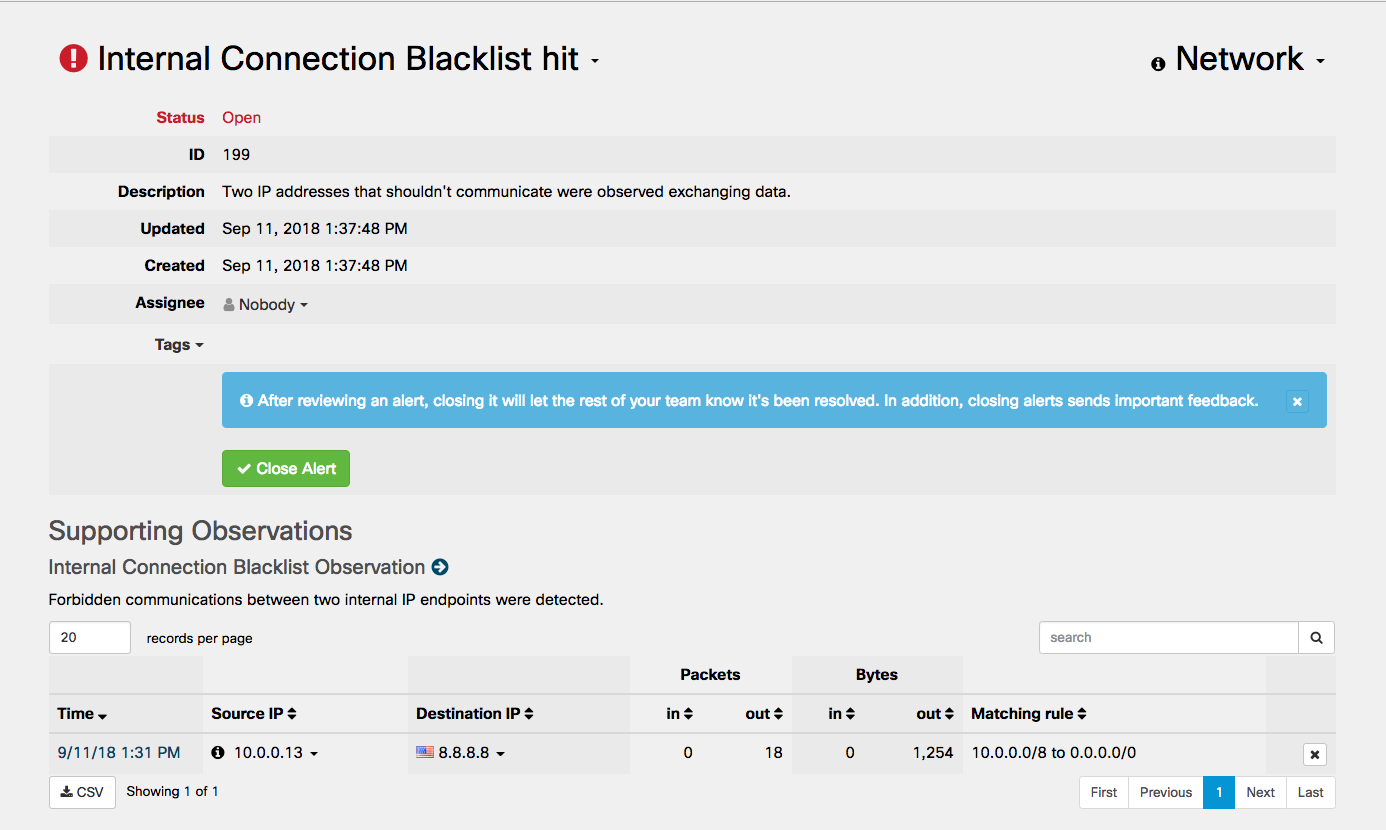

This policy violation alerting framework allows you to be fully accountable for all network prohibited network traffic that will inevitably transit your network laterally or through an egress point. Firewall rules, hardening standards and compliance policies should be adhered to but how can you be certain that they are? Human error, lack of expertise and troubleshooting can and will easily lead to a gap in your posture and Stealthwatch Cloud is the second line of defense to catch any violation the moment that first packet traverses a segment using a prohibited protocol. It's not a matter of IF your posture will be compromised but WHEN.
To learn more about Stealthwatch Cloud, visit cisco.com/go/stealthwatch-cloud
 Tags chauds:
security analytics
Segmentation
Tags chauds:
security analytics
Segmentation