































To evade detection, attackers will often live-off-the-land by using pre-installed binaries like powershell.exe and communicating with legitimate cloud services like dl.dropbox[.]com. The recently released Secure Firewall feature, Encrypted Visibility Engine (EVE), is well-suited for detecting these types of stealthy evasion. EVE extracts two primary types of data features from the initial packet of a network connection:
EVE then identifies the client process by using machine learning built on top of an extensive collection of labeled data that is updated daily, allowing EVE to identify malicious, encrypted traffic even when it is destined for a trustworthy service.
EVE's ability to distinguish between clients enables it to identify malicious use of benign domains. As a concrete example, a recent Talos Threat Roundup provided indicators for DarkKomet that included dl.dropbox.com (note: this indicator included the caveat "Does not indicate maliciousness"). Alerting on this domain would obviously generate many false positives, but EVE can cut through the false positives by incorporating the NPF.
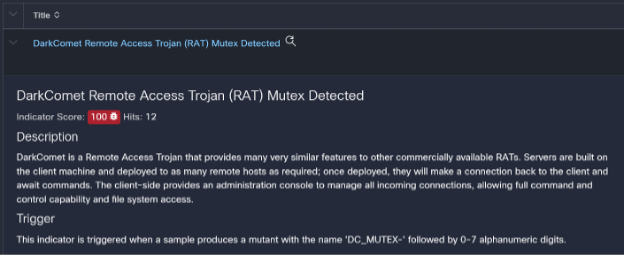
We analyzed a recent DarkKomet sample that was submitted to Cisco Secure Malware Analytics. The sample communicated with dl.dropbox[.]com over TLS using the default Windows TLS library, and EVE correctly classified the connection as originating from a malicious executable. While most traffic using the default Windows TLS library is benign and most traffic destined to dl.dropbox[.]com is benign, the combination of the two features skews heavily towards malicious binaries over the past several months and EVE's machine learning backend leverages these trends.
EVE's training set is updated daily based on hundreds of millions of new network samples annotated with their endpoint ground truth. The relationship between endpoint processes, NPFs, and destinations is dynamic and necessitates a continuous data collection strategy. For this reason, we have devoted a significant amount of time and energy into building out a comprehensive dataset that correlates the network data features needed by EVE at runtime with the endpoint ground truth provided by the Network Visibility Module. We have additionally partnered with Cisco Secure Malware Analytics to collect a similar set of data features as used by samples flagged as malicious.
This data collection allows EVE to continuously learn about the latest trends relating network-based data features with their endpoint process. In the above example, maintaining up-to-date machine learning models was critical because Internet Explorer traffic previously polluted the predictive power of the Windows TLS NPFs, but this issue has since resolved itself due to Microsoft's push to the Edge browser.
The Encrypted Visibility Engine provides enhanced network visibility and control even in situations where the server is trustworthy. EVE originally targeted encrypted protocols like TLS and QUIC, but we have recently added support for HTTP. While HTTP is not an encrypted protocol, the EVE concepts of simultaneously analyzing the NPF/server information and continuous data collection have proven valuable. This is especially true given the trend of benign processes and operating systems moving away from unencrypted HTTP, which makes the class imbalance issues that plague network threat detection less of a concern.
We have several new EVE-related features in the pipeline so stay tuned and, in the meantime, check out these references to learn more:
We'd love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Instagram
Facebook
Twitter
LinkedIn
 Tags chauds:
En vedette
Artificial Intelligence (AI)
incident response
Machine Learning (ML)
Cisco Secure Firewall
threat detection
Cisco AI/ML
encrypted traffic
Tags chauds:
En vedette
Artificial Intelligence (AI)
incident response
Machine Learning (ML)
Cisco Secure Firewall
threat detection
Cisco AI/ML
encrypted traffic