























 Image: Getty
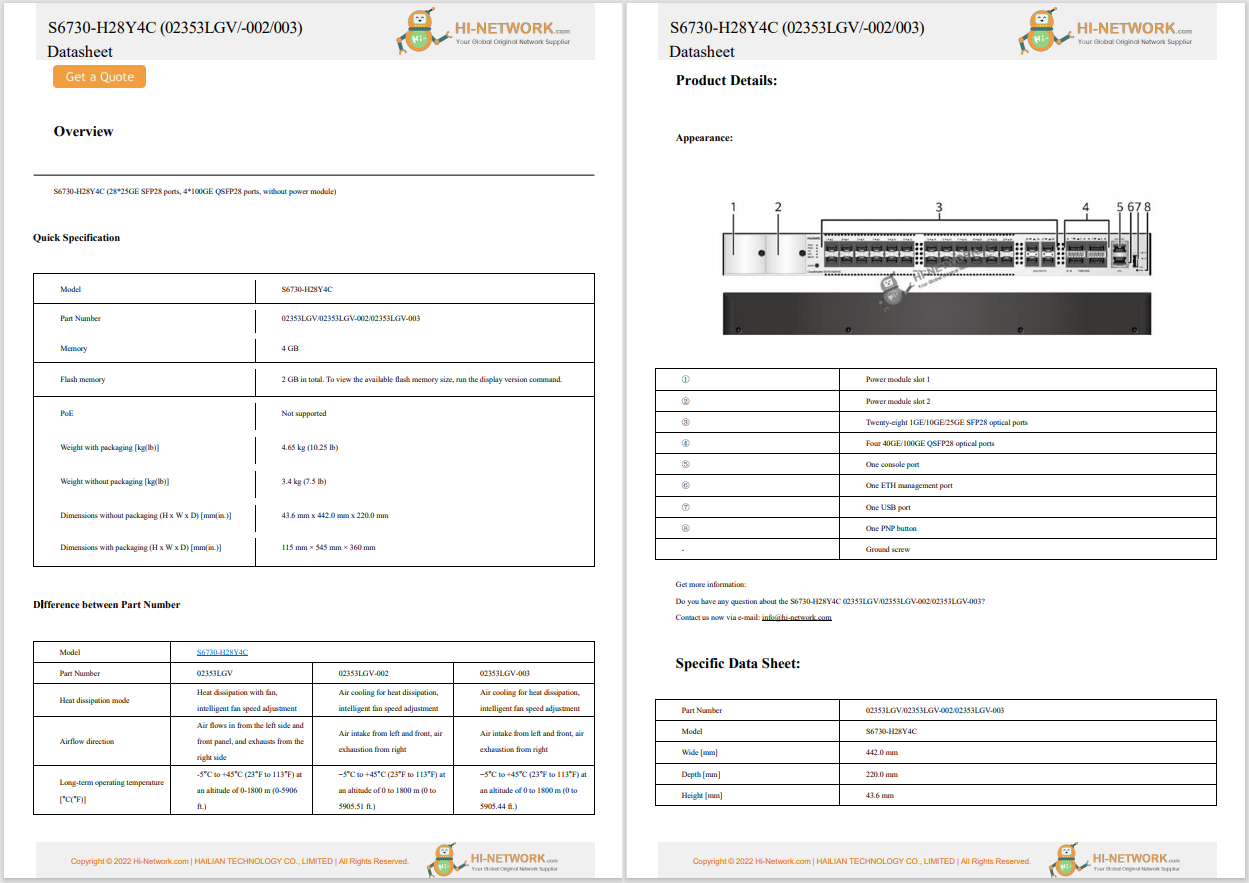
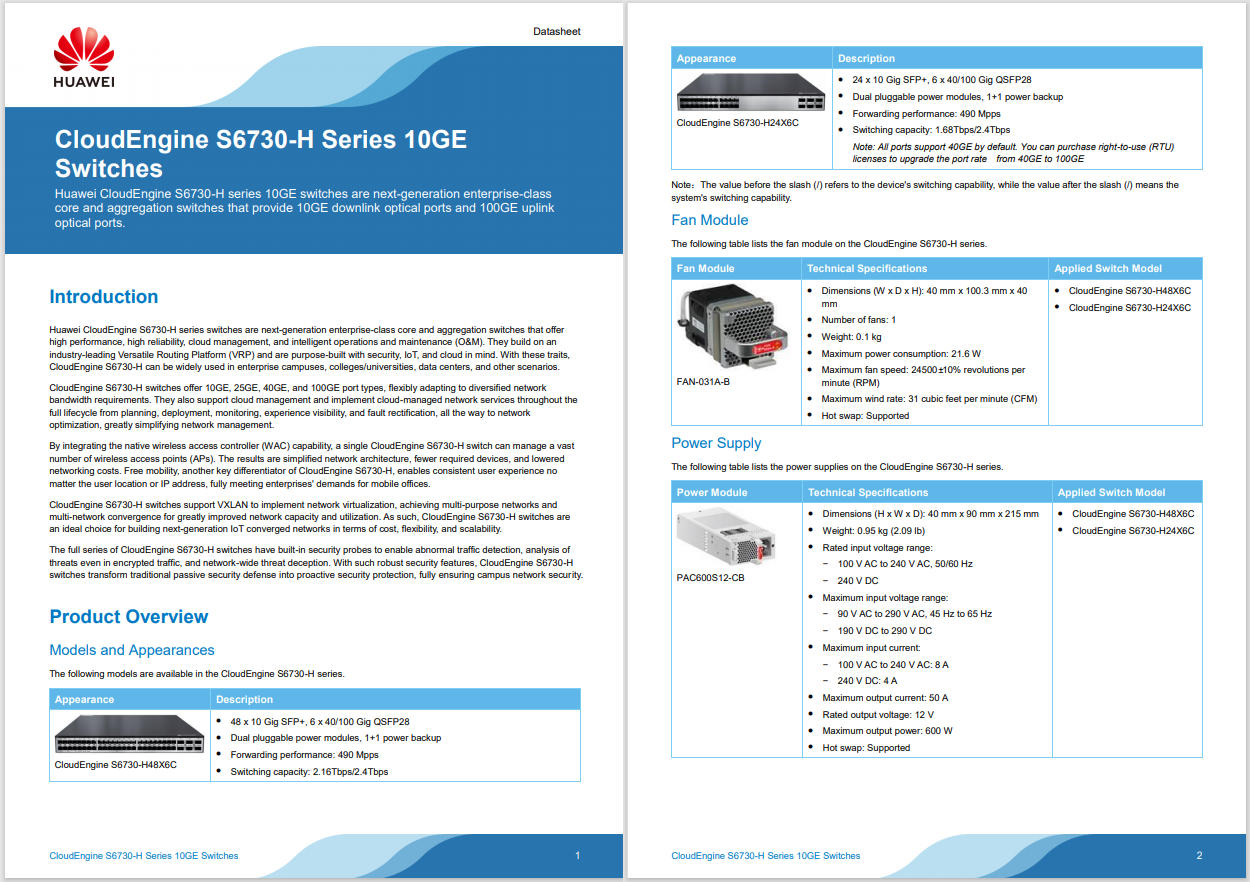
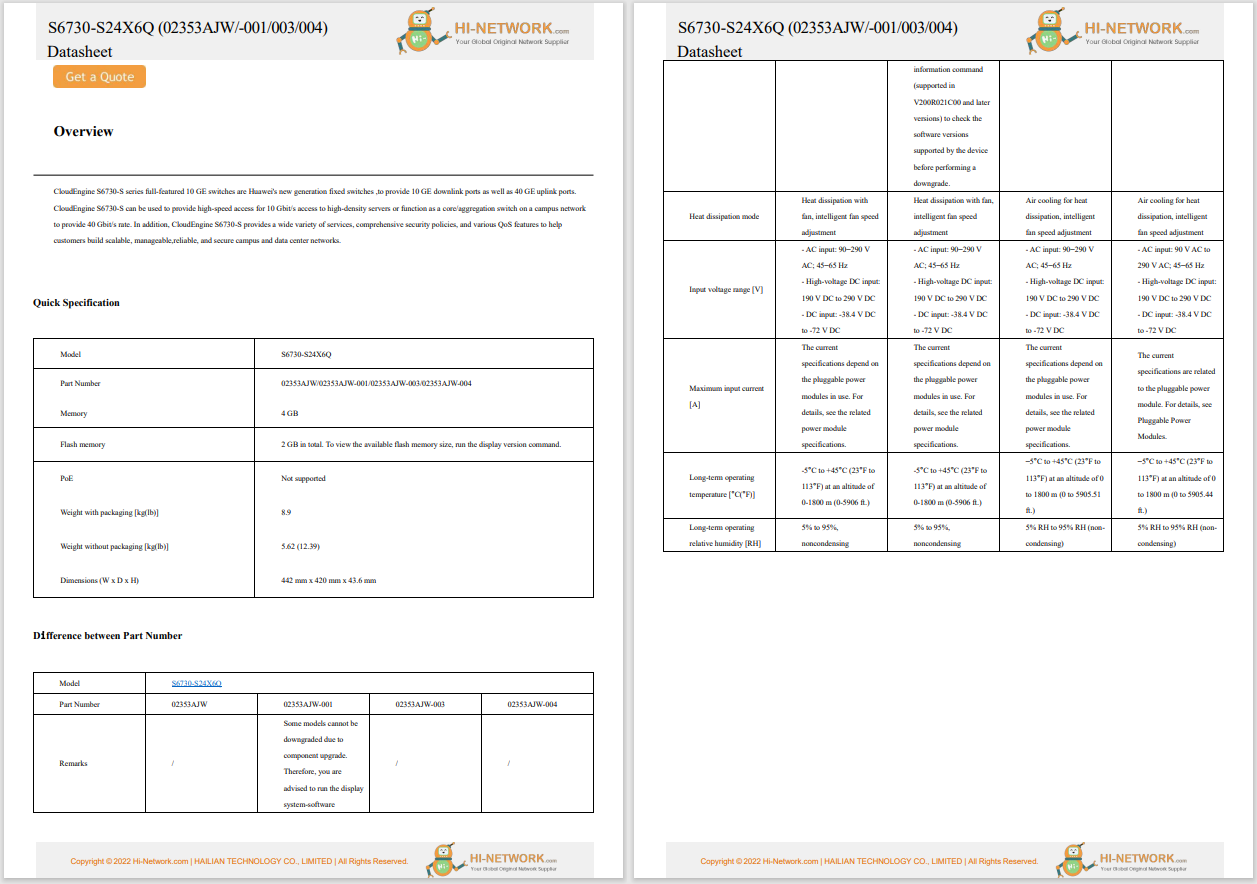
Image: Getty The US Cybersecurity and Infrastructure Agency (CISA) has warned organizations to check recently disclosed vulnerabilities affecting operational technology (OT) devices that should be -but aren't always -isolated from the internet.
CISA has released released five advisories covering multiple vulnerabilities affecting industrial control systems discovered by researchers at Forescout.
These certifications can help you enter an industry with a high demand for skilled staff.
Read nowForescout this week released its report "OT:ICEFALL", which covers a set of common security issues in software for operational technology (OT) devices. The bugs they disclosed affect devices from Honeywell, Motorola, Siemens, and others.
SEE:Phishing gang that stole millions by luring victims to fake bank websites is broken up by police
OT is a subset of the Internet of Things (IoT). OT covers industrial control systems (ICS) that may be connected to the internet while the broader IoT category includes consumer items like TVs, doorbells, and routers.
Forescout detailed the 56 vulnerabilities in a single report to highlight these common problems.
CISA has released five corresponding Industrial Controls Systems Advisories (ICSAs) which it said provide notice of the reported vulnerabilities and identify baseline mitigations for reducing risks to these and other cybersecurity attacks.
The advisories include details of critical flaws affecting software from Japan's JTEKT, three flaws affecting devices from US vendor Phoenix Contact, and one affecting products from German firm Siemens.
The ICSA-22-172-02 advisory for JTEKT TOYOPUC details missing authentication and privilege escalation flaws. These have a severity rating of 7.2 out of 10.
Flaws affecting Phoenix devices are detailed in the advisories ICSA-22-172-03 for Phoenix Contact Classic Line Controllers; ICSA-22-172-04 for Phoenix Contact ProConOS and MULTIPROG; and ICSA-22-172-05 for Phoenix Contact Classic Line Industrial Controllers.
The Siemens software with critical vulnerabilities are detailed in the advisory ICSA-22-172-06 for Siemens WinCC OA. It's a remotely exploitable bug with a severity score of 9.8 out of 10.
"Successful exploitation of this vulnerability could allow an attacker to impersonate other users or exploit the client-server protocol without being authenticated," CISA notes.
OT devices should be air-gapped on a network but often they're not, giving sophisticated cyber attackers a broader canvass to penetrate.
The 56 vulnerabilities identified by Forescount fell into four main categories: insecure engineering protocols, weak cryptography or broken authentication schemes, insecure firmware updates, and remote code execution via native functionality.
The firm published the vulnerabilities (CVEs) as a collection to illustrate that flaws in the supply of critical infrastructure hardware are a common problem.
"With OT:ICEFALL, we wanted to disclose and provide a quantitative overview of OT insecure-by-design vulnerabilities rather than rely on the periodic bursts of CVEs for a single product or a small set of public, real-world incidents that are often brushed off as a particular vendor or asset owner being at fault," Forescout said.
SEE: Ransomware attacks: This is the data that cyber criminals really want to steal
"The goal is to illustrate how the opaque and proprietary nature of these systems, the suboptimal vulnerability management surrounding them and the often-false sense of security offered by certifications significantly complicate OT risk management efforts," it said.
As the firm details in a blogpost, there are some common faults that developers should be aware of:
 Tags chauds:
technologie
La sécurité
Tags chauds:
technologie
La sécurité