























The Middle East region is quickly emerging as a new, dynamic player in the world of cybersecurity regulations. As countries in the region diversify their economies beyond the traditional oil and gas sectors and embrace a digital future for its citizens and residents, new regulations, laws and frameworks are being introduced to ensure protection in the new digital world.
These frameworks, aimed at bolstering the cybersecurity practices across many public and private sector organizations, introduce several mandatory controls and risk management practices which are required for various businesses operating in the region with the intention of increasing cyber resilience.
As a member of Cisco Talos Incident Response, we often get to operate within these frameworks when engaging with our customers during Emergency Response activities or during proactive engagements such as Table Top Exercises, IR Playbook or IR Plan creations.
This blog will delve into the evolution of these regulations, examining the catalysts that prompted their inception and the subsequent impact on shaping the digital landscape.
The State of Qatar's cybersecurity regulatory framework consists of legislations, international standards and strategy guidelines placed within various cybersecurity frameworks, introduced across different strategic and business sectors. The primary body, responsible for cybersecurity policies, within the State of Qatar is the National Cyber Security Agency (NCSA) which was established in 2021 to facilitate the development and proposal of cybersecurity policies and regulations across the country. Several pieces of legislation cover the cybersecurity of IT systems and personal data and are directly applicable to different cybercrime laws. There are two key laws applicable in the State of Qatar are:
While these laws closely guard various cybersecurity aspects related to business and individuals, Qatar's cybersecurity landscape also includes multiple frameworks and guidelines applicable within the country. Three are described below:
Released in 2014, this document outlines initiatives undertaken by the Qatari government to protect key assets and identify risks related to critical information infrastructure (CII). The overall strategy focuses on five main objectives, ranging from building safeguards for the CII to establishing legal frameworks that create a safer cyberspace. It also includes strategies focused on setting up a collaborative environment aimed at building and cultivating national cybersecurity capabilities. The overall theme of this strategy is based on the understanding that cybersecurity is a shared responsibility, and that many government entities, businesses and individuals need to come together to create an environment that is resilient to cybersecurity incidents. The key controls, established within this framework, can be broken down between public and private sector responsibilities. The state, for example, issues legislations such as the Cybercrime Prevention Law (2014) or Personal Data Protection Law (2016) that all individuals and organizations in Qatar should be following. On the other hand, organizations can directly address the outlined strategy by applying the following controls across a few key pillars:
Safeguard national Critical Information Infrastructure (CII)
Implement efficient incident response mechanisms and recovery proceedures
Develop and cultivate national cybersecurity capabilities: Build a skilled workforce, invest in research and development and strengthen national cyber defense capabilities
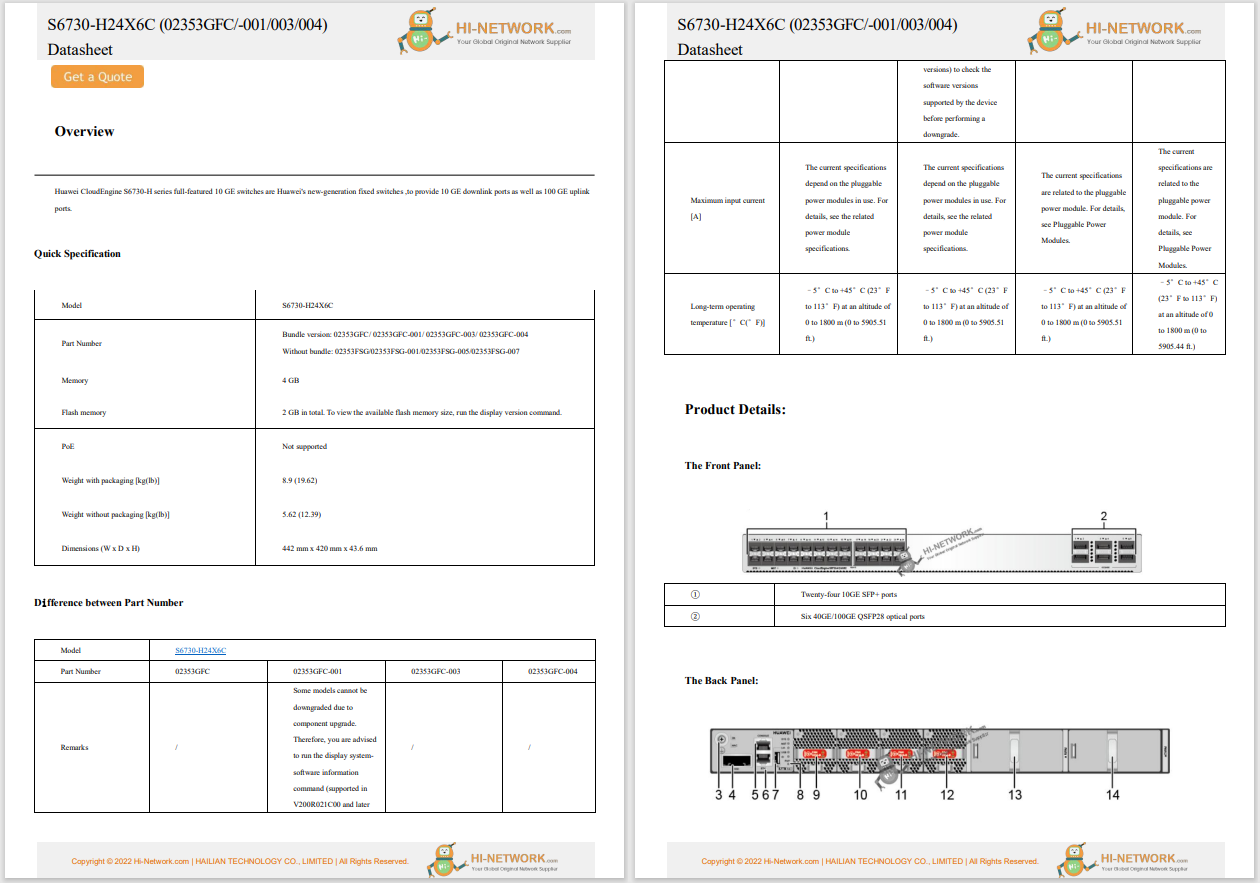
Developed by the Supreme Committee for Delivery & Legacy (SCDL) ahead of the 2022 FIFA World Cup, the QCF provides a set of best practices and controls for organizations to enhance their cybersecurity posture when participating in major events. Controls are mapped to various international standards such as ISO 27001, NIST SP 800-53, ISA62443, PCI-DSS and GDPR. The focus of the framework is predominantly on 14 different capabilities ranging from establishing an appropriate governance to application of security controls in the cloud.
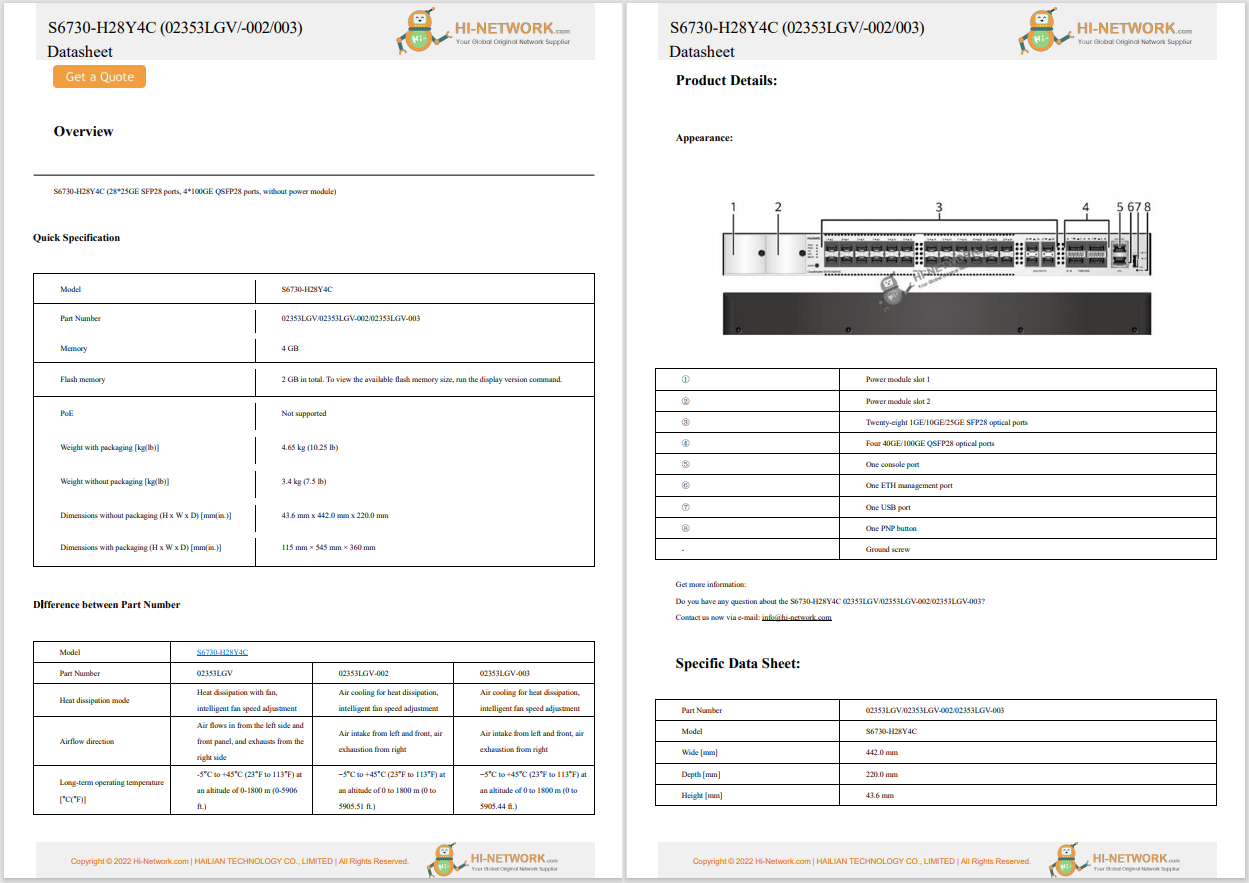
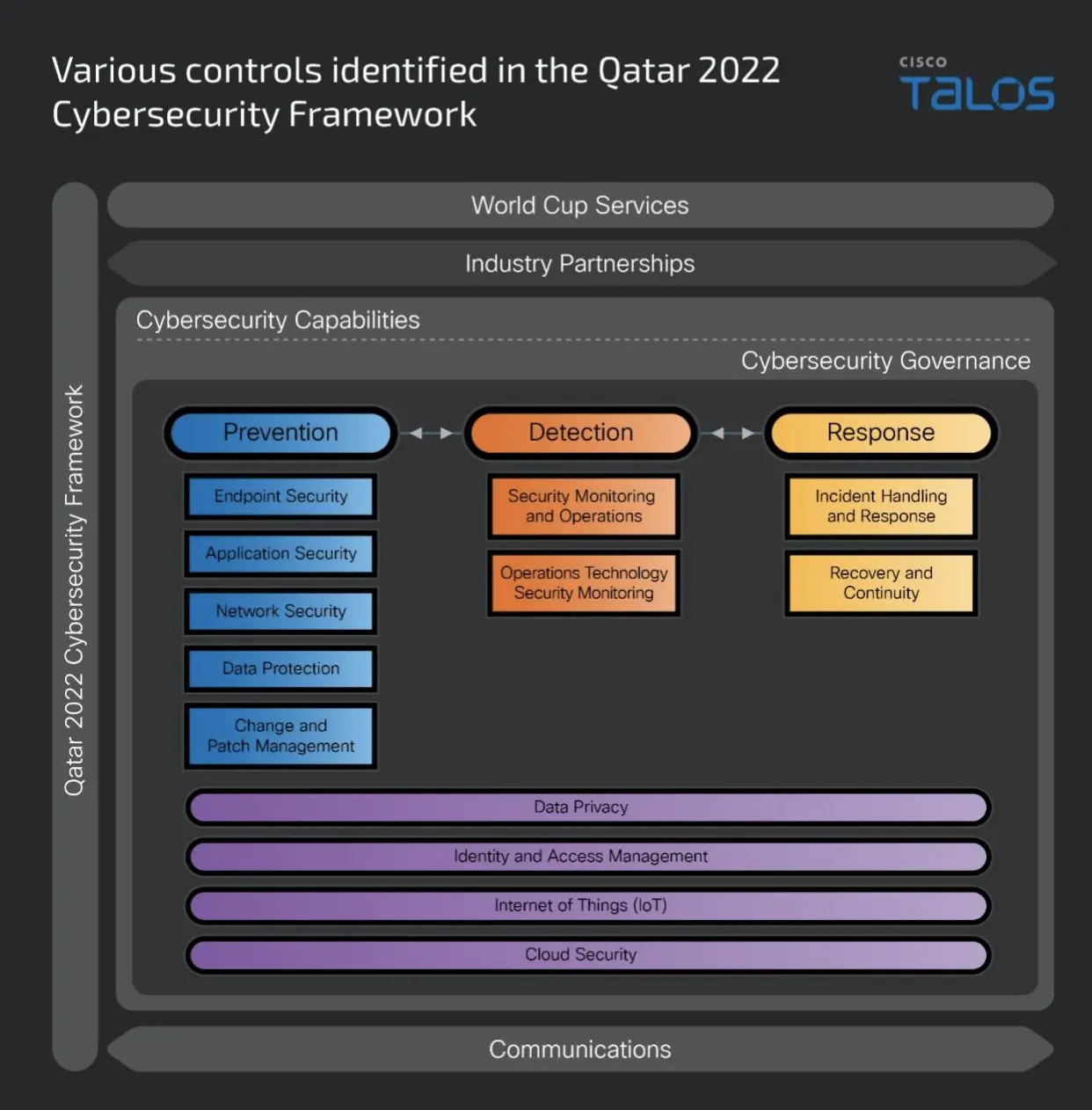 A breakdown of various controls identified in the Qatar 2022 Cybersecurity Framework
A breakdown of various controls identified in the Qatar 2022 Cybersecurity FrameworkThis framework introduced the need to have a widely established risk management strategies that address technical controls, such as ensuring that threats can be detected on all manner of devices such as laptops or servers (requirement 3.2), and capabilities to identify, audit, remediate and test various security strategies, such as hardening of the systems, minimizing risks through establishment of relevant internal frameworks and controls that also rely on presence of appropriate staff (i.e., requirements 4.2 and 5.2). Various controls and assessment requirements are further broken down into major domains with each presenting requirements for how successful controls should be planned, deployed, managed and controlled throughout the lifetime of an event. Where feasible, specific elements of an QCF are mapped to controls present in other standards such as National Information Assurance Standard or ISA62443.
This recent standard introduced several controls to technical, business and governance aspects of any organization operating in the State of Qatar, including third parties and subcontractors that are specifically called out in the scope of the standard (section 2.2). The standard focuses on key areas such as data governance, data security, technical and organization controls. It prioritizes four key principles:
Another important aspect of the standard is the requirement to classify the data that is stored within the organization and the requirement to protect such data with specific controls which are applicable though proactive risk management. It should be noted that this standard operates in conjunction with National Data Classification Policy (2023) to create a synergy between information security and data classification. Each domain and control set have a set of mandatory and optional controls which leaves a scope for flexibility in how controls might be applied within a given organization, as not every possible domain might be applicable, or it may be applicable just in part. Although organizations can apply the standard on a voluntary basis, the National Cyber Security Agency also offers a certification process which assesses the compliance with the standard.
Released in 2024, this strategy document builds on the framework established in 2014 and emphasizes the centralization of security governance under a single organization, the NCSA. The framework is guided by six principles, ranging from shared responsibility, where everyone is accountable for their cybersecurity practices, to a focus on collaboration and coordination among various stakeholders in Qatar's cybersecurity landscape. These guiding principles underpin the five pillars of the framework, each linked to specific strategic goals, including building a resilient cybersecurity ecosystem and fostering legislation and innovation in a data-driven economy. Each pillar can be further broken down into specific objectives that will guide both private and public organizations in achieving greater security maturity through accreditations, education, research, development, and innovation in cybersecurity applications. While some objectives and pillars focus on domestic development, there is also a strong emphasis on forming regional and international partnerships.
Similarly to the State of Qatar, the Kingdom of Saudi Arabia (KSA) have introduced legislations and frameworks aiming to ensure that cybersecurity application is as widespread as possible and applicable across as many sectors as possible in line with the digitization objectives. Protection from digital threats is one of the objectives of Vision 2030 which puts emphasis on digital society living in a safe cyberspace supported by the Kingdom's e-government. The two key laws applicable in the Kingdom of Saudi Arabia are:
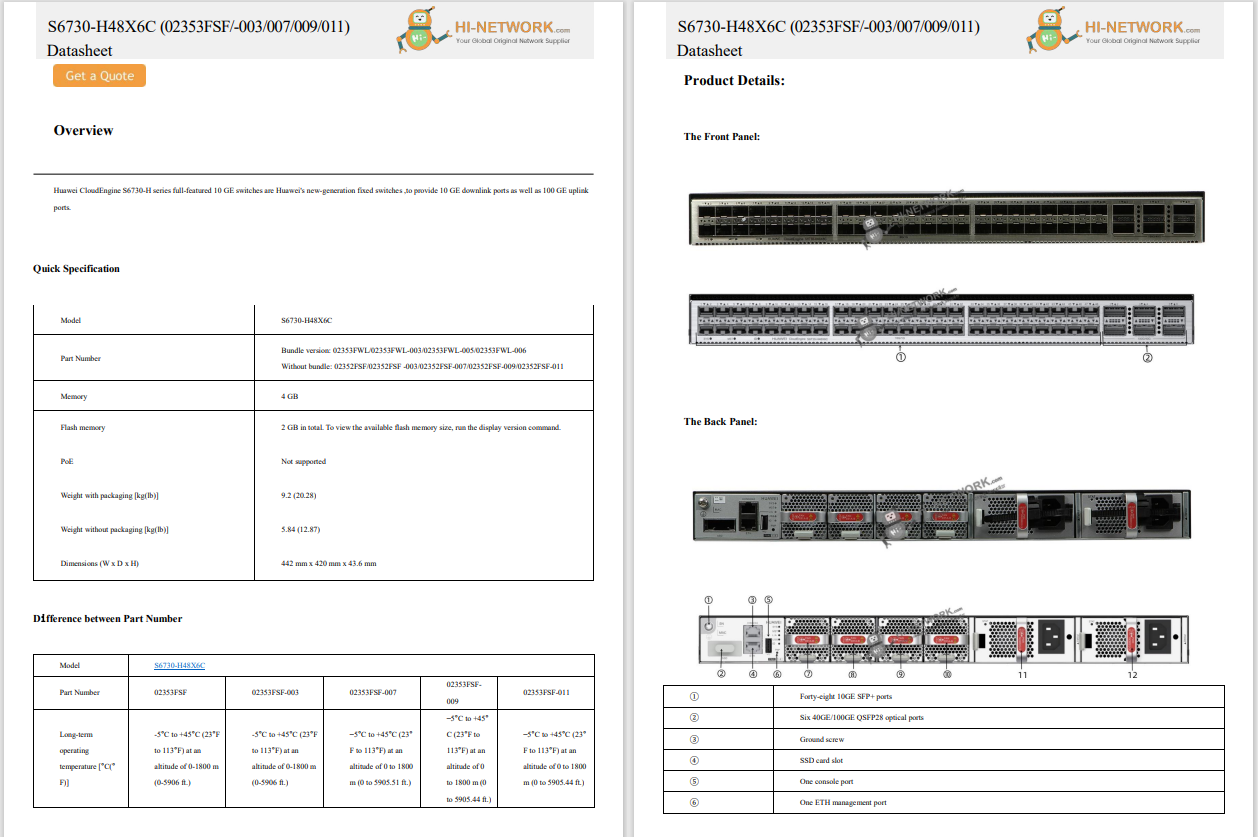
As part of the National Cybersecurity Strategy (NCS), the National Cybersecurity Authority (NCA) was established in 2017 to regulate and improve the cybersecurity landscape in the KSA with the objective to oversee the application and development of cybersecurity regulations across the Kingdom. The strategic positioning of the NCA allows it to not only create legal, policy and regulatory environments, but actively participate and engage with regulated bodies through assessments or assistance with information sharing exchanges and other applicable partnerships.
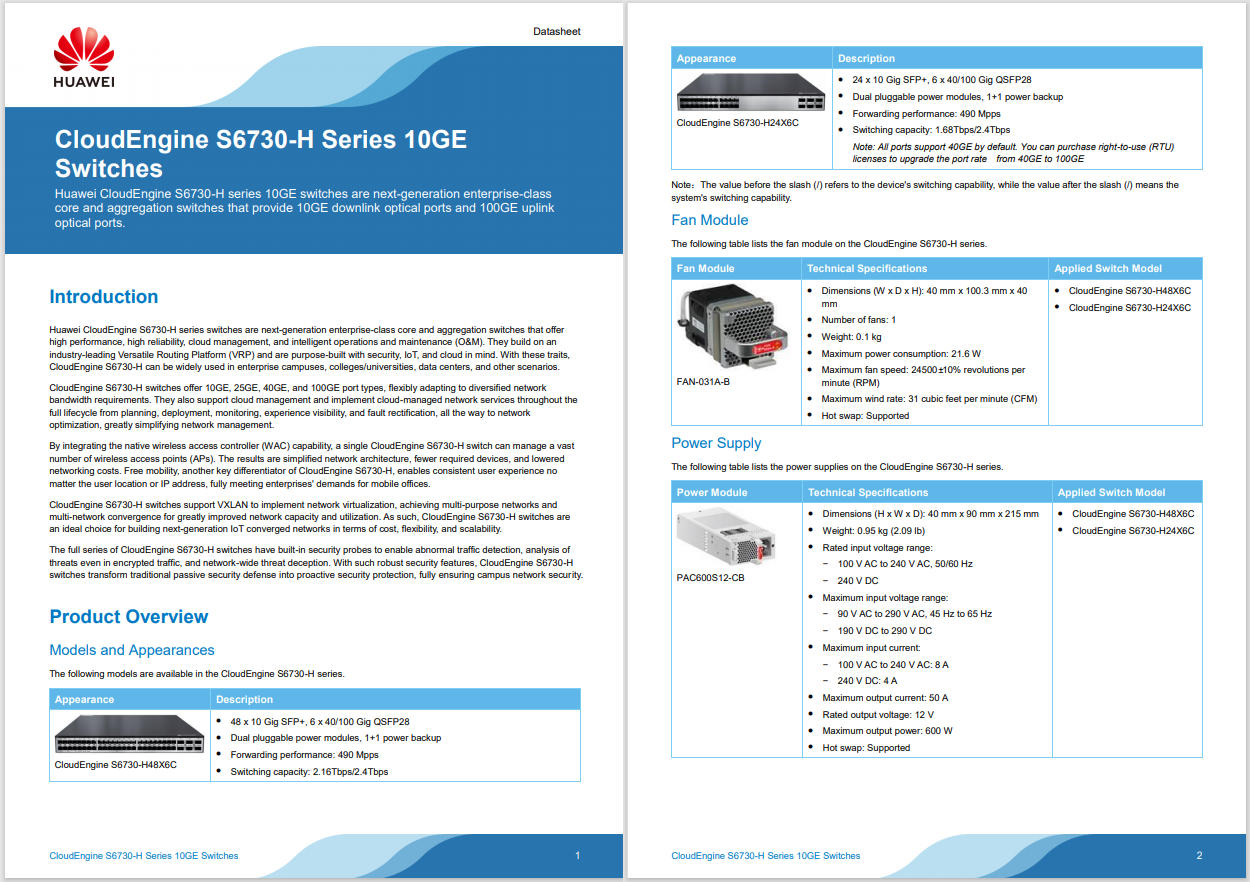
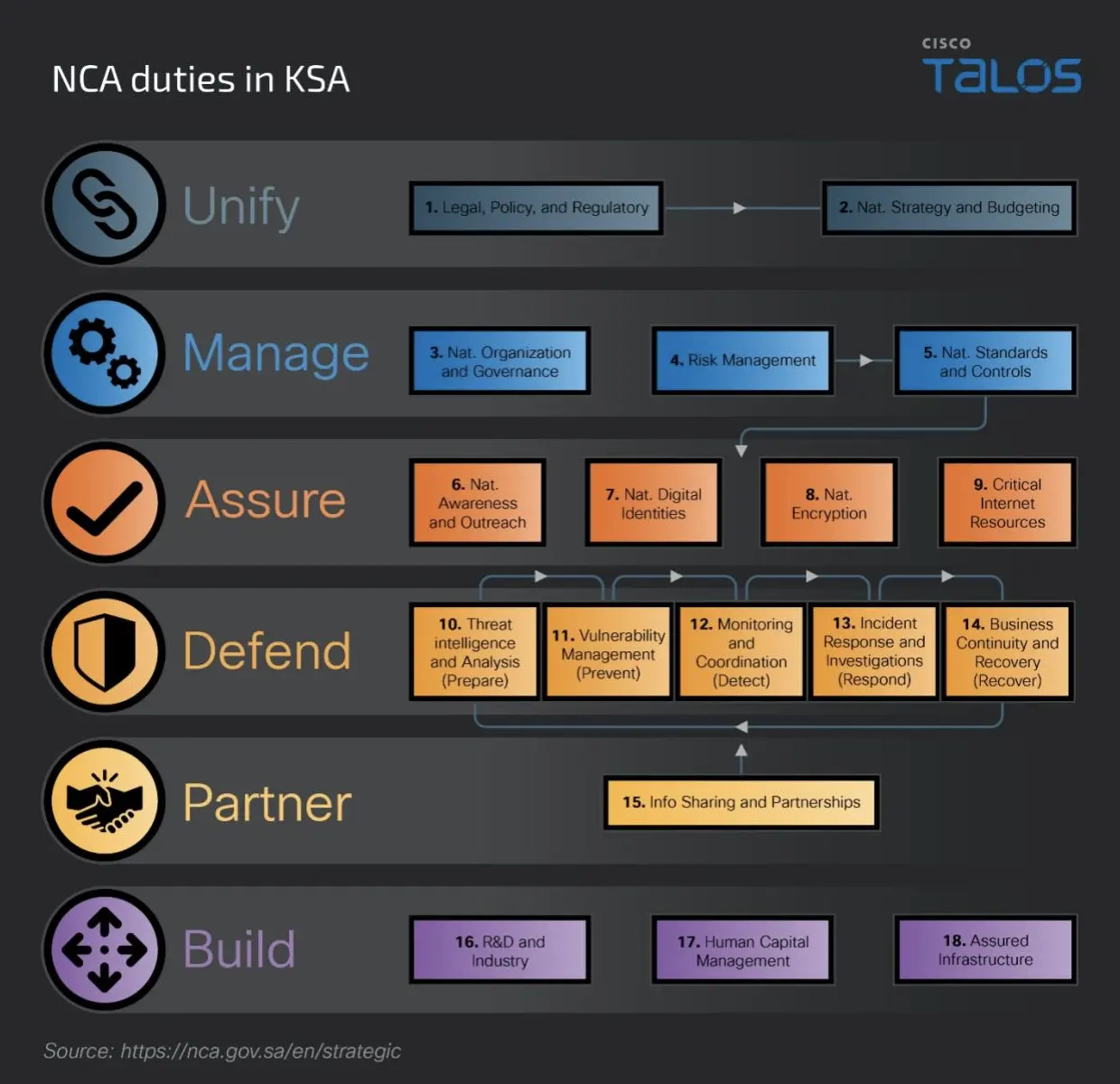 A breakdown of NCA duties in KSA
A breakdown of NCA duties in KSAThe NCA carries out major responsibility for development and the application of various controls and frameworks across different verticals in the KSA and breaks down several shared responsibilities into frameworks, which collaborate at various levels in the public and private sectors.
The NCSS is a cornerstone strategy that outlines several key principles that the Kingdom of Saudi Arabia will follow to enhance the country's cybersecurity. The strategic goals of the NCSS are to unify cybersecurity governance under one body (the NCA), create a partnership environment to collaborate and perform cybersecurity research, defend the country from cyber threats and build national and industry cybersecurity capabilities. The NCSS outlines how the Kingdom will approach the development of cybersecurity in the future and sets out administrative control over this process.
Outlines a set of mandatory minimum cybersecurity requirements for organizations, public and private, operating within the Kingdom of Saudi Arabia. These controls serve as the foundation for protecting critical infrastructure, government services, and private businesses from cyberattacks and threats. There are 114 different controls established across five main domains:
Cybersecurity Governance
Focuses on establishment of mechanisms that that drive the adoption of cybersecurity measures. The key controls deployed within this standard are:
Cybersecurity Defense
Focuses on building controls to protect systems and networks from unauthorized access, malware, and other threats. The key control in this section starts with establishing a detailed asset register, which highlights devices at risk, among the devices owned by the business and ensures that appropriate visibility is granted to systems under management. These controls come in many forms such as ensuring that identity access, mobile devices, perimeter, and network devices are well configured, hardened and segregated. In addition to building technical controls, this document also focuses on ensuring that process perspective is taken into consideration and so, there are multiple requirements around, for example, penetration testing, incident response and vulnerability management, and how these types of engagements should be performed.
Cybersecurity Resilience
Focuses on building measures to recover from cyber attacks and minimize disruptions to ongoing operations though a requirement for Business Continuity Management (BCM) and ensuring that appropriate business continuity processes are created and can be followed in an event of a major business disaster.
Third-party and Cloud Computing Cybersecurity
Addresses security considerations resulting from engaging with third parties or cloud services. When it comes to third parties, which might augment cybersecurity capabilities of an organization, there are specific requirements related to non-disclosure agreements (NDAs), communication cadence and the need for third parties to comply with organizational policies. Cloud computing aspect of this domain, on the other hand, requires creation of appropriate policies, classification of data that will be uploaded to the cloud and separation of cloud environments internally from other tenants. ECC calls for storage of the data inside the Kingdom of Saudi Arabia.
Industrial Control Systems Cybersecurity
Addresses controls applicable to industrial control systems (ICS) and critical infrastructure (CI). This part of the ECC Standard calls for creation of a strictly segmented ICS environment that will be continuously monitored for potential incidents and safety. Configuration and hardening are also required, along with patch and vulnerability management processes, which must be implemented to ensure that cybersecurity is upheld within ICS deployment.
CSCC is an extension to the ECC providing additional guidance towards organizations that operate or own critical systems. To be compliant with CSCC, the ECC requirements also need to be fulfilled. There are 32 other main controls applied across similar domains as in the ECC standard. CSCC places emphasis on the necessity to ensure that the controls, deployed and configured in alignment with the ECC, undergo a rigorous testing process. This involves regular assessments to review applicable security configurations and address any identified deficiencies. The overarching goal is to maintain a robust cybersecurity framework by continuously testing and validating the effectiveness of the implemented controls in accordance with the ECC standard and adding additional layer of verification or additional controls.
Similarly to CSCC, the CCC controls are an extension of the ECC and aim to provide a set of minimal requirements, which cloud service providers (CSP) and cloud service tenants (CST) need to fulfil to ensure that data, stored in the cloud, is safe. This framework divides controls into these applicable to cloud service providers and cloud service tenants. While some controls are identical, the general theme of the framework puts a requirement for providers to inform tenants about cybersecurity controls that are applicable to data stored in the environment, and for tenants to have applicable policies which they can compare and contract with controls provided by CSP. There also are strict requirements on controls such as personnel vetting, data storage and disposal, access and policies and procedures that need to be created and applied to cloud assets.
The Sultanate of Oman started to examine their cybersecurity practices in 2010 with the creation of the Oman Computer Emergency Readiness Team (OCERT), which monitors cyber threats, investigates incidents and provides guidance to organizations based on the latest cybersecurity laws and standards applicable in the country. The laws that are applicable in the Sultanate of Oman support Oman's Vision 2040, which puts a strong emphasis on digital transformation and presence of technology across the economy. The two key laws applicable in the Sultanate of Oman are:
Oman's flagship data protection law, granting individuals rights over their personal data and imposing obligations on organizations handling the data. In terms of application, organizations must adopt data protection measures in line with the PDPL, including obtaining consent, implementing security controls and responding to data subject requests.
This cornerstone law criminalizes the unauthorized access, modification or destruction of data and other common cybercrime such as fraud or violation of privacy.
The following guidelines and standards, aimed mostly at government and public-sector entities, are available in the Sultanate of Oman:
The BCS controls standards outline the set of basic and necessary security controls that should be applied across government organizations in Oman. Starting with access control, the standard breaks down applicable cybersecurity guidance into twelve major control groups and offers a high-level guidance on how each of the major domains should be applied. Each security control outlines how it should be established, validated, and introduced within the organisation. For example, when "Incident Management" controls are mentioned, BSC outlines how the process of identifying, analysing, responding, and recovering from security incidents should be documented and what kind of skills or mechanism should be implemented to protect confidentiality, integrity, or availability of the information assets. The BCS framework also outlines a checklist that should be applied within every organization.
The standard aims to ensure that basic minimal security controls are applied for the database systems and their users such as administrators, developers, and database managers. It outlines several security controls, specifically related to databases, such as the need to segregate duties or privileges of various database users to ensure that database `root` is not granted to low-level users or enablement of encryption within the applications communicating with the database. Specific security controls such as data classification, change management and audit should also be applied to database servers.
Applicable to all custodians of information on behalf of the Sultanate of Oman, this policy outlines high-level information security principles that should be applicable to all organizations. It calls for creation of Information Security Committee which might consist of existing steering committees or senior management, looking after data within any government organization. The committee should oversee the development and implementation of security program, applicable within the organization, and implement specific steps such as risk management, data classification, awareness training, incident management and business continuity.
This high-level guideline framework outlines the overview of various cybersecurity governance principles and requires regulated bodies to establish cybersecurity governance within organization. The framework offers a guidance on how governance process should be established within the business, in a form of six key steps which aim to help in identifying current, desired, and future state of cybersecurity within a government organization. The breakdown of the guidelines is as follows:
Cloud and Hosting Services Standard (CHSS) presents a breakdown of requirements applicable to Cloud Service Providers (CSP). At a high level, the CSPs not only need to comply with international security frameworks such as ISO 27001, ISO27017 and ISO 270018 and control matrices presented by Cloud Security Alliance (CSA) and PCI-DSS when hosting payment solutions. An important emphasis of this framework is on how data is handled, classified, and stored within a cloud environment and how access to such environments is provided. A CSP is also to be accredited by a "Third-Party Assessment Organization" which will audit, and access compliance of cybersecurity controls related to contingency planning, monitoring and the results of various assessments such as penetration testing.
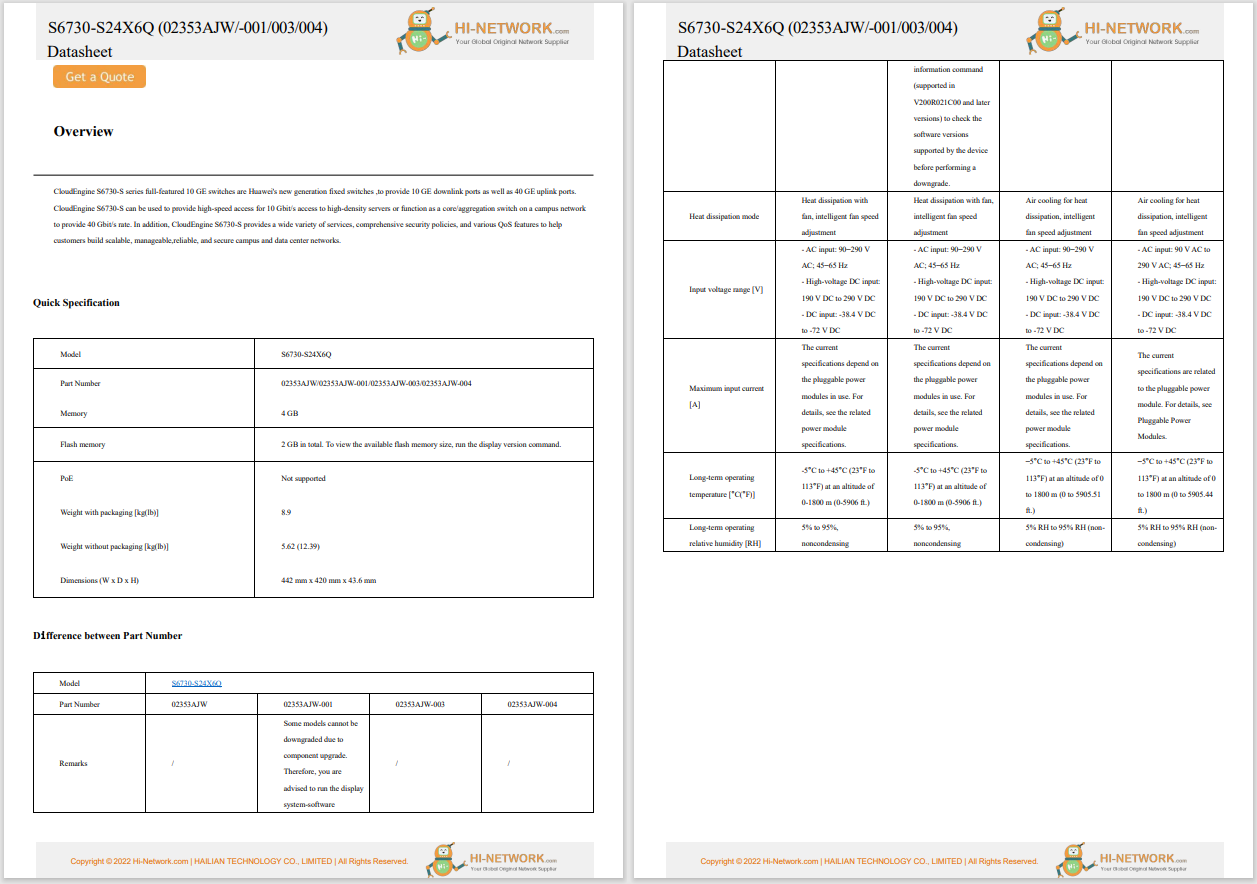
To better demonstrate how each country creates and applies cybersecurity regulations the following table was devised based on available frameworks, law and applicable guidelines at the time of writing this blog:
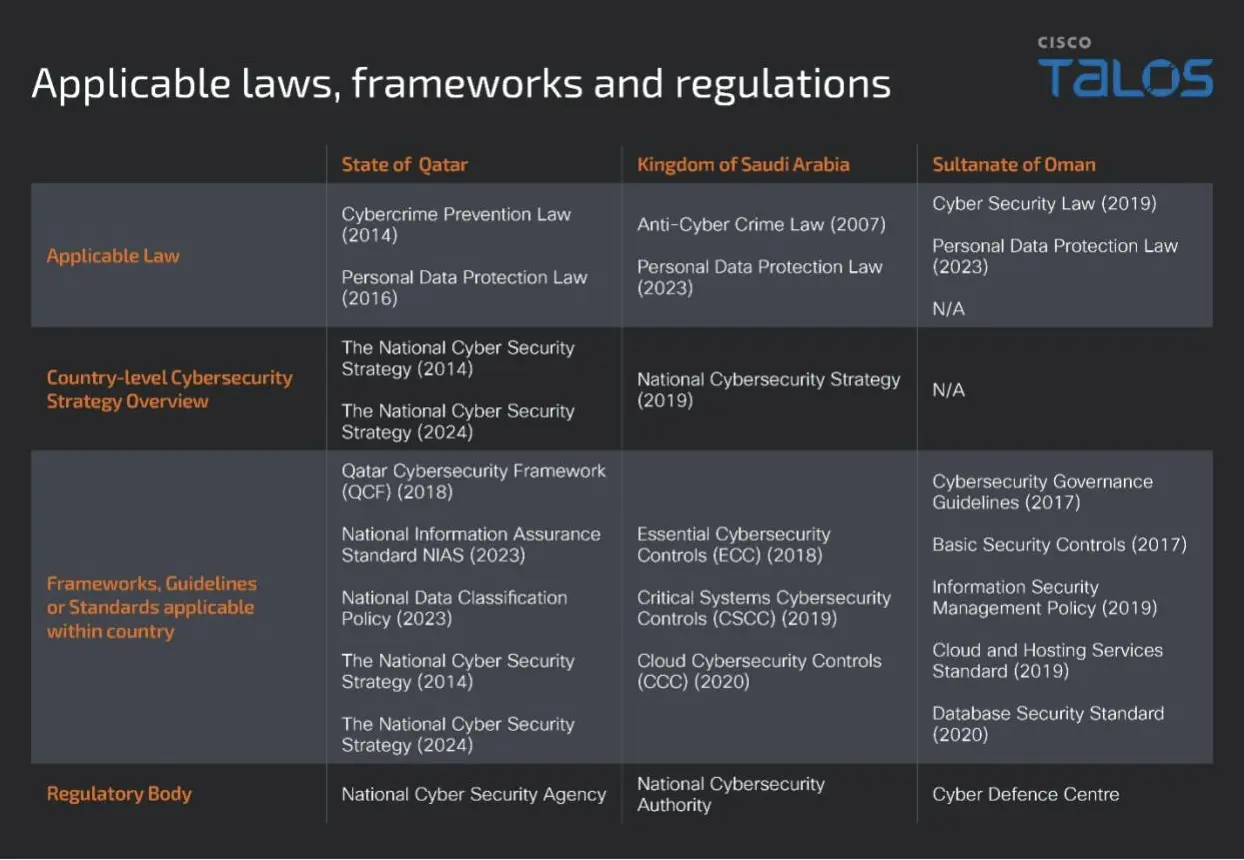
Although every listed country introduced their own flavours of cybersecurity controls, spread across many standards, frameworks and laws, there are some commonalities between all countries mentioned in this blog post:
We'd love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
 Tags chauds:
Tags chauds: